|
New Zealand small businesses are currently facing a new and often misunderstood threat to their livelihood. COMPUTER SECURITY. Over HALF of all small businesses in New Zealand was targeted by ransomware in 2020. (Ref.) That's 50% of us! As cybercrime cannot be seen, and can be hard to imagine, we tend to think, is it really that bad? Small business computer security is an often overlooked challenge, by both IT providers and small businesses owners themselves, but we have made it our mission to improve the security of New Zealand Small Businesses. "...there are approximately 530,000 small businesses in New Zealand representing 97% of all firms. They account for 28 per cent of employment and contribute over a quarter of New Zealand's gross domestic product." (ref.) We think this sector of our community should get the same protection from cybercrime as big business gets. So we are going to show you how to achieve this for yourself. Step One: Maintenance Maintenance. This word can seem a little to much like the word 'Housework'. Its a bit boring, a bit repetitive, and really who knows what you should actually do. But, it is the first step to securing your network, and without it, your network will never be secure. Security vulnerabilities are found daily, so to keep your equipment safe, manufacturers release patches and updates to their software to keep up to date. Equipment and software that is out of date becomes insecure over time, so keeping up to date is a vital part of your security protocol. 1. Create an Asset Registry The first step to maintaining your equipment is to establish what equipment you have. Write down a list of every computer, laptop, server and any infrastructure equipment you have. This can include:
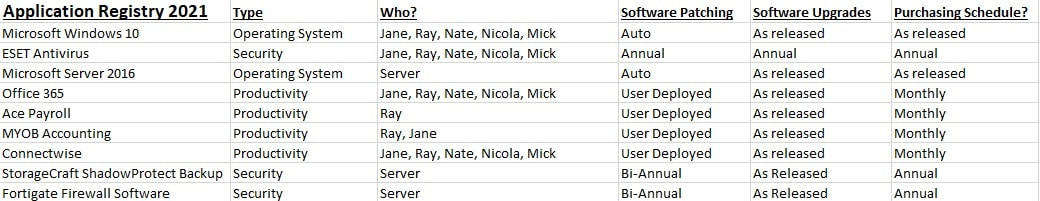
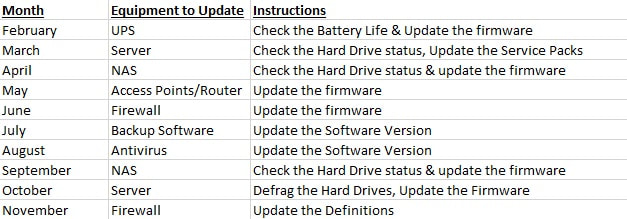
2. Add in Applications to your Registry Once you have established a registry of equipment, you need to add into the list your applications, as these often need to be considered separately. Start with the Operating Systems. Likely these will patch themselves automatically, but if you are not often connected to the internet, then this will need specific attention. Then consider your infrastructure applications, such as Antivirus, SPAM or Malware applications, and Backup software. These will likely require manually updates. Antivirus software will require definition updates as well as software updates. Lastly add in your industry software, such as Payroll, Accounting, Creative and Productivity software. Note: You will not need to include applications that are solely accessed via the web (such as Xero) as these are updated for you. 3. Purchasing Application Maintenance Applications will often not be able to be updated if they are not on a maintenance agreement, or simply may require the upgrade to be purchased once available. This particularly applies to antivirus software, backup software and operating systems, but can also apply to payroll, accounting and other industry software. Include details of the purchasing requirements in your register. An example of an application registry. 4. Determine what needs updated For each type of equipment or application, you will need to determine what requires updating on a regular basis. This will be different for each type of equipment or application. For example, a workstation requires the O/S to be updated (patched) but most likely the O/S will update itself. A router or switch will likely require the firmware to be updated. Check the user manual for each piece of equipment/application to assess what maintenance tasks are recommended. 5. Make a Roster Many, many hours can be lost in maintaining equipment, so we recommend creating a roster for these tasks. Some equipment/applications will require patching regularly, such as operating systems or firewall appliances. Other things, such as Access Points, NAS, or switches likely only require firmware updates once a year. An example of an update schedule Now that you have a clear indication of the equipment and applications that you need to update, what you need to update, and a schedule to stick to, all you need to do now is follow your schedule to ensure your network is kept up to date and secure. Check out for Secure Your Small Business Network Part Two: SECURITY MEASURES for the next stage to securing your network. More Resources:
www.cert.govt.nz/business/guides/secure-your-small-business-network/ www.cisco.com/c/en/us/solutions/small-business/resource-center/security/network-security-checklist.html https://docs.microsoft.com/en-us/troubleshoot/windows-client/networking/set-up-your-small-business-network https://www.business.govt.nz/risks-and-operations/it-risk-and-avoiding-scams/protecting-business-data/
0 Comments
|
AuthorVictoria Murgatroyd-McNoe has been working in the IT sector helping businesses achieve their technology goals for over 20 years. Archives
November 2022
Categories |
|
Universal Support
|
Discover
|
|


 RSS Feed
RSS Feed
