|
Annual Security Assessment
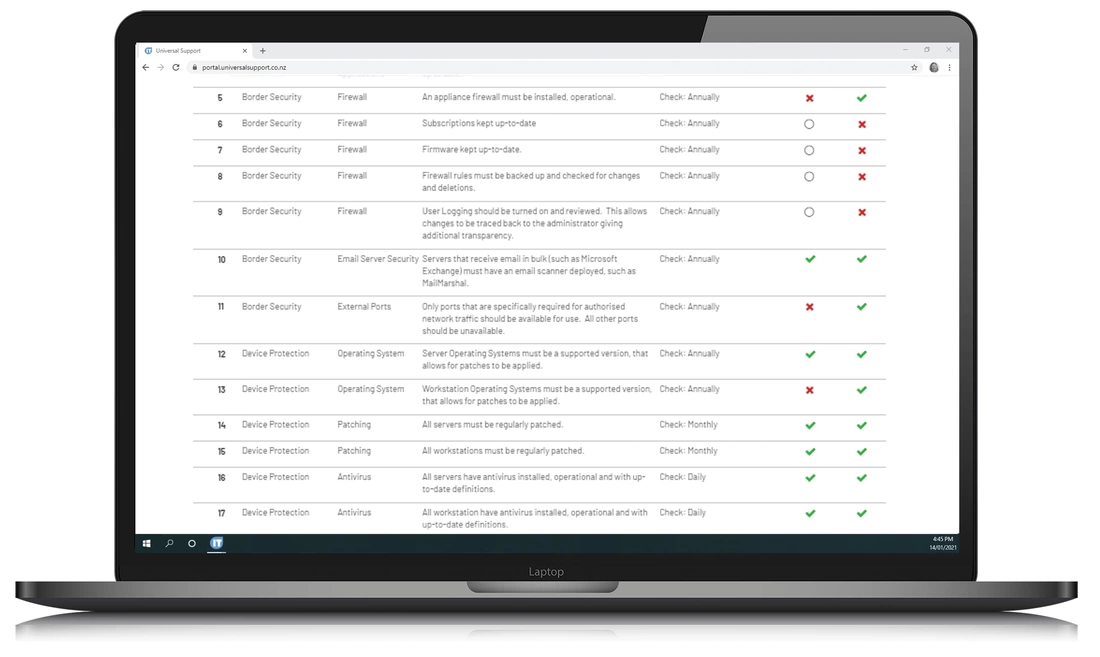
To ensure you are aware of the levels of security measures that are employed on your network, we prepare a Security Assessment that outlines each part of your network that requires a security policy.
We explore concepts such as conditional access, password management, open/closed ports, spam detection, phishing detection, Microsoft 365 security, identity management, user access, global administration, application management, external access, disaster recovery and security awareness to determine your risk profile, and to build the most appropriate security strategy for your organisation.
We repeat this process annually, to make sure your network is up to date with the latest developments.
|
|
Security Standard
We follow the NIST framework to assess the security standards of your network. Once a year we take the time to deep dive into your network to ensure that the current security standards are being met. During the year, we monitor various parts of your security structure for changes and updates.
|
Activity
As part of our 24/7 monitoring system, we monitor daily activity into your firewall, your antivirus and the event logs, SPAM & Spoof mail, mail volumes and failed logins for unusual activity. This helps us to ascertain if your security measures remain effective.
|
Security Updates
As the security landscape changes constantly, we compare the changes in the industry to changes on your network, and adjust your network to take into account the differences. Microsoft and other software companies are quick to keep up to date with the latest threats, and are providing additional tools daily to combat any new challenges. We keep up to date with the latest tools available, and deploy them on your network so that your network is always is the most protected state it can be.
|
|
FAILED LOGINS
REJECTED
|
PHISHING EMAILS
QUARANTINED
|
SPOOFED EMAILS
QUARANTINED
|
All security measures
|
Server Specific Software Compliance
Workstation Installs Compliance Local Admin Access Compliance End User Applications Compliance Appliance firewall Compliance Firewall Subscriptions Compliance Firewall Firmware Compliance Firewall rules Compliance Firewall User Logging Compliance Email Scanner Compliance Open Port Compliance Server Operating Systems Compliance Workstation Operating Systems Compliance Server Patch Compliance Workstation Patch Compliance |
Antivirus Compliance
Workstation Antivirus Compliance Backup Device Login Compliance Backup Device Password Policy Compliance External Backup software Compliance Internal Backup Software Compliance Cloud Backup Software Compliance External Backup Frequency Compliance Internal Backup Frequency Compliance Cloud Backup Frequency Compliance External Backup Encryption Compliance Internal Backup Encryption Compliance Cloud Backup Encryption Compliance RDP Compliance RDP Software Compliance |
Remote Email Access Compliance
Static IP Compliance Digital Certificate Compliance Wireless Security Compliance Wireless User Access Compliance Guest Login Compliance VLAN Compliance Mobile Encryption Compliance Network Management Compliance BYOD Compliance Security Awareness Compliance Password Complexity Compliance Password Expiry Compliance Password Length Compliance Password History Compliance Previous Password Compliance Lockout Compliance |
Lockout Period Compliance
Admin Name Compliance Global Admin Compliance Admin Password Policy Compliance Multifactor Authentication Compliance Office365 User Access Compliance Email Authentication Compliance Role Based Compliance Annual Security Assessment Daily Event Log Checks Daily SPAM Checks Daily Spoof Mail Checks Mail Volume Checks Failed Login Checks Login Attempt Checks |