|
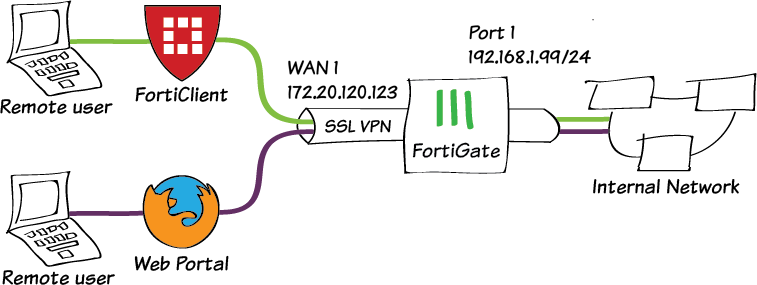
Photo Credit: Photo by Guido Jansen on Unsplash Your firewall is a generally forgotten piece of your networking equipment, but we would like to remind you of the amazing things that it does for your network, and why you should LOVE your firewall. As June is Firewall month (and so is November!) we wanted to tell you all about why we love your firewall, and why you should too!  COVID-19 and Your Firewall The coronavirus pandemic of 2020 has sent us all reeling, but it has highlighted some surprising things, such as how our slowdown has positively impacted our environment. (How the Climate is benefiting from Covid-19) Similarly, your firewall was quietly working hard, making your work-from-home experience seamless. What is a Firewall? Your firewall is a small device that will likely be sitting under the stairs, or in the cupboard at the back of your office, with all the other equipment you are assured is important, but you are not really sure what it does. Your firewall is one of those light-flashing mystery appliances. Your firewall is an internet traffic device. Every time you send something by email, or look at something on the internet, your firewall processes that request, and checks it before it sends the signal onto its destination. Your firewall also checks traffic coming in, such as received mail and remote access. Your firewall checks everything, including web browsing, email, music streaming and video conferencing. All-Powerful Firewall Your firewall has the power to deny access, either in or out of your network, if it decides that the traffic doesn't adhere to its strict rules, or if it suspects that the traffic is not doing what it claims to be doing, such as malicious threats to the network. Your firewall can also check the traffic for viruses, malicious content in emails and it can also check which websites you are travelling to, and deny you access. If you don't want users on your network to be scrolling through facebook or going to the TAB site, or any other non-work approved site, the firewall can stop them. Thank Goodness for VPN's Due to Covid-19 we have all been encouraged to work from home, and we have taken this onboard in our droves. However, this meant getting access to the information on the network at the office as quickly as possible. Luckily your firewall was at the ready with its VPN capabilities. Your firewall can create for you a Virtual Private Network (VPN) which allows a secure connection from your PC at home to the firewall at the office and then onto your work PC or to your server. Your Firewall VPN secures this connection using encryption and tunneling (sorry, what!?). Let me explain. A VPN prevents your data from being intercepted, monitored, or altered by anyone. The tunnel hides your IP address, which can otherwise be used to identify you. Instead of your real location, the sites you visit will only see the location of the VPN server you are connected to. The encryption scrambles the data being transmitted, so only the intended destination can read the data. If your data gets intercepted, it can't be read. Once connected via a VPN to the office, its just like being at the office. You can see your mapped drives, you can access network resources, you can clear your mail and print to your home printer, all while at home, in your pjamas (we wouldn't do that, would we?!). There are other methods to remotely connect to the office but the connection from home using the Firewall VPN is the most secure and reliable way to go about this and the best part is that there is no additional cost, as it is built into your firewall. Image courtesy of the Fortinet Cookbook: https://docs.fortinet.com/document/fortigate/6.2.0/cookbook/724772/ssl-vpn-multi-realm Show Your Firewall Some Love
As with any technology, your firewall needs occasional updating to keep up to date with the latest threats and to get the benefit of the enhancements manufacturers create, so they can keep ahead of their competition. If your firewall is under Managed Services, or Universal Support, these updates will happen without an intervention from you (we will let you know when they will happen). For those not under contract, we have a firewall blitz every June and November, so if you have updates ready, we will let you know they are ready to be installed. If you haven't heard from us in a while, check in with us, just in case you have been missed from our list, and check out what updates you may need installed. Updates, What Updates? In June, we concentrate on firewall firmware, backing up your firewall rules and checking your open ports. Firmware should be updated to make sure there are no vulnerabilities on the firewall itself that can be exploited by malicious users. The firewall rules should be backed up regularly, so that if a problem happens on your firewall, we can easily restore you to a version of the rules we know worked well. The open ports on your firewall should be checked at least once per year, to make sure changes haven't happened over the year. This can happen when a temporary service requires a port to be opened, but the port is not closed once that service has stopped. These errant ports can be used as a stepping stone into your network, so its best to keep them closed if they are not being used. In November, we concentrate on the firmware again, and also the Antivirus & AntiSpam definitions. If you are using them, the Antivirus and Antispam firewall technologies acts as an additional check (on top of your usual Antivirus & AntiSpam protections), and while these definitions don't require constant updates, updating them annually is good practice. Do You Love Your Firewall as Much as We Do? Ok, probably not. But hopefully you now have some idea why we love them, and why you should keep them up to date! If you have any questions, as always, drop us a line at sales@decision1.co.nz.
0 Comments
New Zealand small business has an enduring love for Pay-As-You-Go IT support. When it breaks, I call you. Easy. The costs are low, and you feel like you have some control. If I don't have a need for you, or I can work it out myself, then there are no costs to me. But pay-as-you-go support is bad for business, so we are moving away from it. How We Got Here In the last 20 years, technology has changed exponentially. In the year 2000, we were mostly concerned with Y2K. Would our computers make it through the change of the century. Companies feverishly bought Y2K compatible machines to ensure their business wouldn't suffer any ill-effects from the year-2000-bug. Nokia released one of their first mobile phones. Windows 2000 was released (but we were all still on Windows 95 & Windows NT). Networks as we know them were in their infancy. The Internet was just coming into its own. Most companies didn't yet have a website. Computer viruses were just starting to take off. IT service companies were starting to come into their own. If you ran an organisation of just about any size, you better be able to pick up the phone and get an IT guy to come and fix your broken PC when you need them. Your PC breaks, the IT guy fixes it. Simple. And it was simple. It was a system that made sense for all involved. Once a fix was applied, or an upgrade was installed, there was very little need for the IT guy in between times, unless you were a large organisation that had these queries all the time, where it made sense to hire someone onto your staff to take care of these things full time. Technology Has Moved OnSecurity Has Moved OnOr rather, those with malicious intent have become increasingly sophisticated. They are constantly on the lookout for networks that have security flaws, trying to find an easy source of income. We make their job easy, by not paying attention to the maintenance of our network. Maintaining your network is also no longer a straightforward task. In the past, basic maintenance of a network meant making sure servers were patched, and the antivirus was checked. Now that devices, software and cloud services are so interconnected, maintenance now looks like patching, upgrading, remediation, skill building, research, documentation, monitoring and auditing. All of these tasks are vital, and if one is not completed, then security flaws start to appear in a network. Security and Maintenance are now the same thing. One does not happen without the other. Maintenance, Maintenance, MaintenanceYou Need to Move with the Technology tooIn a Pay-As-You-Go support arrangement, the maintenance of a network is left up to you. If you are in this arrangement, and you are not performing the maintenance tasks yourself, then your network is not secure. In this case, you have either already been attacked, or will be in the future. Its a case of when, not if. If you are in this arrangement you are a the highest level of security risk you can be. Change this now. Don't wait. In a partial Pay-As-You-Go arrangement which includes server maintenance, you are in a better position, but its still not great. Your network is more than just your server, and if you are not maintaining your other devices, then you are still very, very, vulnerable. In a network with a Fully-Covered server, with everything else on pay-as-you-go, then your situation is also better, but you are still vulnerable, as you have closed one door, but left many others open. It can not be expressed more strongly, if digital security is something vaguely important, (and it should be your top business priority) network maintenance is your only option. Don't Get CaughtDon't get caught with old technology, and old ideas about what the technology can do for your business. Technology is considered an asset in most organisations. It provides us with a wonderful array of functions, that most of us would not do without anymore. Don't allow your technology to be a detriment to your business. Get your network maintained and get it secured. What Is The Answer?Our solution to this problem is Universal Support. Monitoring, Maintenance, Security & Support are all rolled into one service.
It is rolled into a single service, because separating the services is no longer a good choice. It is rolled into a single service because separating the services is no longer possible, as each service crosses paths with other services. It is rolled into a single service so knowledge about the network and how it serves the organisation can be built up over time. It is rolled into a single service so skills specific to the network can be built up over time. It is rolled into a single service because everything works better when a network is approached as a single entity. |
AuthorVictoria Murgatroyd-McNoe has been working in the IT sector helping businesses achieve their technology goals for over 20 years. Archives
November 2022
Categories |
|
Universal Support
|
Discover
|
|



 RSS Feed
RSS Feed
