|
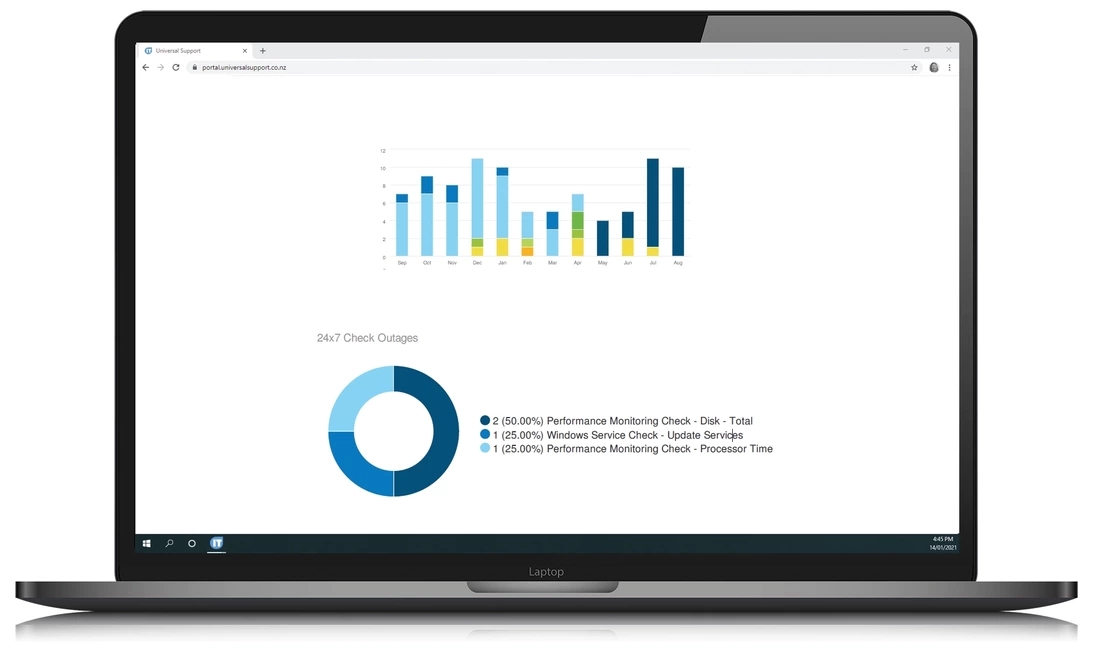
Monthly Health Reports
Each month we will send you a variety of reports that outlines the health of your server and network in general. This report details the status of your antivirus for the previous month, backup jobs that were performed for the previous month, server uptime, windows services availability and disk drive growth.
|
|
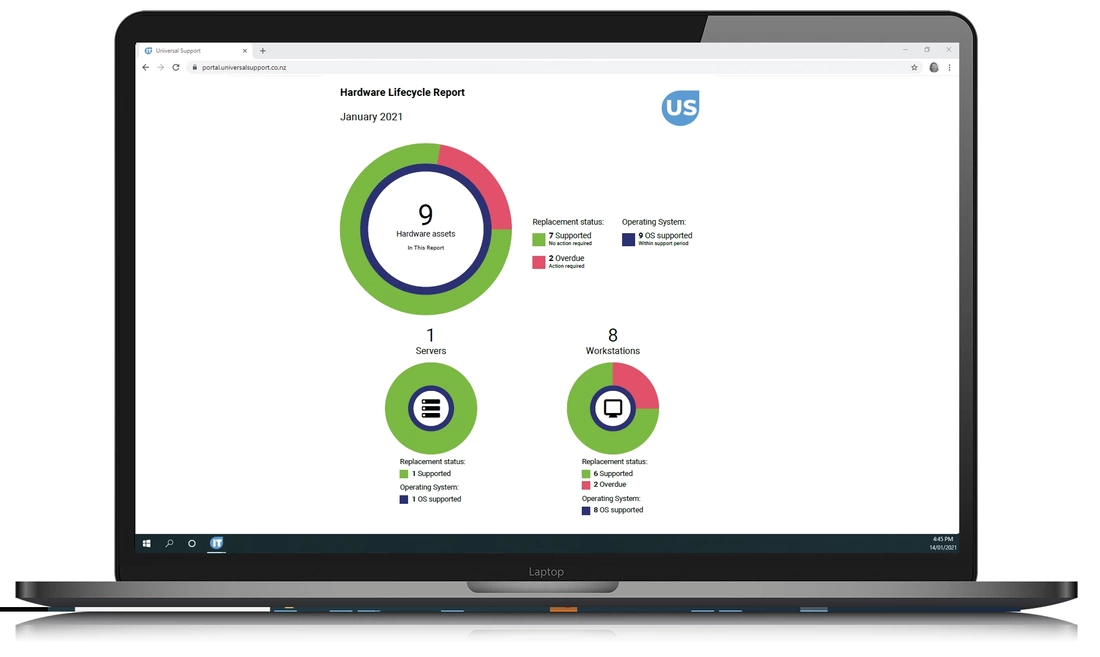
Asset Review
Once per year, we will update your asset review. This review will detail the current status of your hardware, and our recommendations for upgrades and replacements. This will also outline your current monthly & annual product commitments, such as Office 365, Antivirus and backup software.
Once prepared, we will present this review to you in person, so that management strategies can be discussed in detail. |
Security Assessment
In addition to the Asset Review we will conduct a full security review once per year. Network security is a fine balance between allowing access to network resources to your staff and denying access to unauthorised users. Over time technologies change, and new strategies can be employed to combat unauthorised access, so a regular review is vital to ensuring your network is secure. This review includes Mobile Device Security, Border security, User Access,, Administrator Rights, & Disaster Recovery.
|
Border Report
The border between your network and the outside world is the most vulnerable part of your business. So you can keep an eye on the activity happening at your border, we generate a variety of reports for you to view activity such as failed logins, spoofing, spam, malware, phishing attacks, risky surfing and others.
|
Priorities Report
Your priorities for your business affect the kind of things you prioritise for your technology. We make sure that we fully understand your priorities so that the road map of your technology matches the roadmap of your business.
|
|
NETWORK
REPORTS
|
SECURITY
REPORTS
|
ASSETS
REVIEWED
|
All details we report for you
|
Hardware replacement status
Operating System support status Hardware support status Hardware specs: : Computer Name : Serial no. : MAke & Model : Operating System version : Age : Purchase Date : Expiry Replacement budget Application Usage Top Application Categories Most Used High Bandwidth Applications Remote Access Applications Used Social Media Applications Used Video/Audio Streaming Used |
Proxy's Used
Peer to Peer Applications Used High Risk Applications in Use Most Active Users Most Used Applications Support Ticket Review Daily Check Ticket Review Maintenance Ticket Review Server Software Security Level User Install Right Security Level Local Admin Rights Security Level End User Application Security Level Firewall Security Level Firewall Subscription Security Level Firewall Firmware Security Level Firewall Rules Security Level Firewall Auditing Security Level Email Server Security Level External Port Security Level |
Operating System Security Level
Patch Security Level Antivirus Security Level Backup Credentials Security Level Backup Software Security Level Backup Setup Security Level Backup Encryption Status Cloud Storage Security Level External Portal Security Level Remote Access Security Level Remote Email Access Security Level Static IP Status Wireless Access Security Level Mobile Device Security Level Password Policy Security Level Administrator Role Security Level Global Admin Security Level Multifactor Authentication Status |
Advanced Threat Protection Status
AP Security Level User Rights and Roles Security Level Web Services Security Level Staff Training Security Level Daily Backup Completed Status Antivirus Operations Status Site Uptime Server Uptime Daily Safety Checks Analysis Outage Analysis Backup Outages 24/7 Outage Checks Status Daily Safety Check Status Failed Login Check Server Disk Drive Growth Patch Install Status Missing Patches |